About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 268 results for "David Moore" clear search
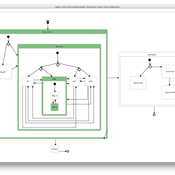
Using Agent-Based Modelling and Reinforcement Learning to Study Hybrid Threats
kpadur | Published Friday, September 20, 2024Hybrid attacks coordinate the exploitation of vulnerabilities across domains to undermine trust in authorities and cause social unrest. Whilst such attacks have primarily been seen in active conflict zones, there is growing concern about the potential harm that can be caused by hybrid attacks more generally and a desire to discover how better to identify and react to them. In addressing such threats, it is important to be able to identify and understand an adversary’s behaviour. Game theory is the approach predominantly used in security and defence literature for this purpose. However, the underlying rationality assumption, the equilibrium concept of game theory, as well as the need to make simplifying assumptions can limit its use in the study of emerging threats. To study hybrid threats, we present a novel agent-based model in which, for the first time, agents use reinforcement learning to inform their decisions. This model allows us to investigate the behavioural strategies of threat agents with hybrid attack capabilities as well as their broader impact on the behaviours and opinions of other agents.
Peer reviewed MicroAnts 2.5
Diogo Alves | Published Thursday, October 16, 2025MicroAnts 2.5 is a general-purpose agent-based model designed as a flexible workhorse for simulating ecological and evolutionary dynamics in artificial populations, as well as, potentially, the emergence of political institutions and economic regimes. It builds on and extends Stephen Wright’s original MicroAnts 2.0 by introducing configurable predators, inequality tracking, and other options.
Ant agents are of two tyes/casts and controlled by 16-bit chromosomes encoding traits such as vision, movement, mating thresholds, sensing, and combat strength. Predators (anteaters) operate in static, random, or targeted predatory modes. Ants reproduce, mutate, cooperate, fight, and die based on their traits and interactions. Environmental pressures (poison and predators) and social dynamics (sharing, mating, combat) drive emergent behavior across red and black ant populations.
The model supports insertion of custom agents at runtime, configurable mutation/inversion rates, and exports detailed statistics, including inequality metrics (e.g., Gini coefficients), trait frequencies, predator kills, and lineage data. Intended for rapid testing and educational experimentation, MicroAnts 2.5 serves as a modular base for more complex ecological and social simulations.
Replica of Turchin's (2003) Metaethnic Frontier model
Paul Smaldino | Published Sunday, February 15, 2026In his 2003 book, Historical Dynamics (ch. 4), Turchin describes and briefly analyzes a spatial ABM of his metaethnic frontier theory, which is essentially a formalization of a theory by Ibn Khaldun in the 14th century. In the model, polities compete with neighboring polities and can absorb them into an empire. Groups possess “asabiya”, a measure of social solidarity and a sense of shared purpose. Regions that share borders with other groups will have increased asabiya do to salient us vs. them competition. High asabiya enhances the ability to grow, work together, and hence wage war on neighboring groups and assimilate them into an empire. The larger the frontier, the higher the empire’s asabiya.
As an empire expands, (1) increased access to resources drives further growth; (2) internal conflict decreases asabiya among those who live far from the frontier; and (3) expanded size of the frontier decreases ability to wage war along all frontiers. When an empire’s asabiya decreases too much, it collapses. Another group with more compelling asabiya eventually helps establish a new empire.
Modeling financial networks based on interpersonal trust
Michael Roos Anna Klabunde | Published Wednesday, May 29, 2013 | Last modified Thursday, November 28, 2013We build a stylized model of a network of business angel investors and start-up entrepreneurs. Decisions are based on trust as a decision making tool under true uncertainty.
Parental choices, children's skills, and skill inequality: An agent-based model implemented in Python
Andrés Cardona | Published Thursday, October 30, 2014The model explores the emergence of inequality in cognitive and socio-emotional skills at the societal level within and across generations that results from differences in parental investment behavior during childhood and adolescence.
Life Cycle Cost of Military Manpower Model
Jonathan Ozik Todd Combs | Published Monday, January 05, 2015We demonstrate how Repast Simphony statecharts can efficiently encapsulate the deep classification hierarchy of the U.S. Air Force for manpower life cycle costing.
Peer reviewed Lithic Raw Material Procurement and Provisioning
Jonathan Paige | Published Friday, March 06, 2015 | Last modified Thursday, March 12, 2015This model simulates the lithic raw material use and provisioning behavior of a group that inhabits a permanent base camp, and uses stone tools.
Exploring organizational learning in innovation networks. An agent-based model
Sandra Schmid | Published Saturday, March 07, 2015This agent-based model represents a stylized inter-organizational innovation network where firms collaborate with each other in order to generate novel organizational knowledge.
Health and social public information office (SPUN) simulation
Emilio Sulis Manuela Vinai | Published Friday, November 06, 2015 | Last modified Saturday, November 07, 2015The program simulate the functioning of an italian health and social public information office (SPUN) on the basis of the real data collected in the first five years of functioning.
HomininSpace
Fulco Scherjon | Published Friday, November 25, 2016 | Last modified Tuesday, October 06, 2020A modelling system to simulate Neanderthal demography and distribution in a reconstructed Western Europe for the late Middle Paleolithic.
Displaying 10 of 268 results for "David Moore" clear search