About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 388 results for "Huw Vasey" clear search
Hybrid agent-based methodology for testing response protocols
Fernando Sancho Caparrini | Published Wednesday, February 03, 2021In recent years we have seen multiple incidents with a large number of people injured and killed by one or more armed attackers. Since this type of violence is difficult to predict, detecting threats as early as possible allows to generate early warnings and reduce response time. In this context, any tool to check and compare different action protocols can be a further step in the direction of saving lives. Our proposal combines features from continuous and discrete models to obtain the best of both worlds in order to simulate large and crowded spaces where complex behavior individuals interact. With this proposal we aim to provide a tool for testing different security protocols under several emergency scenarios, where spaces, hazards, and population can be customized. Finally, we use a proof of concept implementation of this model to test specific security protocols under emergency situations for real spaces. Specifically, we test how providing some users of a university college with an app that informs about the type and characteristics of the ongoing hazard, affects in the safety performance.
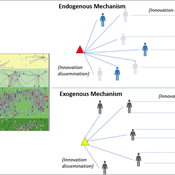
Peer reviewed Modelling Agricultural Innovations as a Social-Ecological Phenomenon
Maja Schlüter Udita Sanga | Published Thursday, November 17, 2022The goal of the AG-Innovation agent-based model is to explore and compare the effects of two alternative mechanisms of innovation development and diffusion (exogenous, linear and endogenous, non-linear) on emergent properties of food and income distribution and adoption rates of different innovations. The model also assesses the range of conditions under which these two alternative mechanisms would be effective in improving food security and income inequality outcomes. Our modelling questions were: i) How do cross-scalar social-ecological interactions within agricultural innovation systems affect system outcomes of food security and income inequality? ii) Do foreign aid-driven exogenous innovation perpetuate income inequality and food insecurity and if so, under which conditions? iii) Do community-driven endogenous innovations improve food security and income inequality and if so, under which conditions? The Ag-Innovation model is intended to serve as a thinking tool for for the development and testing of hypotheses, generating an understanding of the behavior of agricultural innovation systems, and identifying conditions under which alternated innovation mechanisms would improve food security and income inequality outcomes.
Using Agent-Based Modelling and Reinforcement Learning to Study Hybrid Threats
kpadur | Published Friday, September 20, 2024Hybrid attacks coordinate the exploitation of vulnerabilities across domains to undermine trust in authorities and cause social unrest. Whilst such attacks have primarily been seen in active conflict zones, there is growing concern about the potential harm that can be caused by hybrid attacks more generally and a desire to discover how better to identify and react to them. In addressing such threats, it is important to be able to identify and understand an adversary’s behaviour. Game theory is the approach predominantly used in security and defence literature for this purpose. However, the underlying rationality assumption, the equilibrium concept of game theory, as well as the need to make simplifying assumptions can limit its use in the study of emerging threats. To study hybrid threats, we present a novel agent-based model in which, for the first time, agents use reinforcement learning to inform their decisions. This model allows us to investigate the behavioural strategies of threat agents with hybrid attack capabilities as well as their broader impact on the behaviours and opinions of other agents.
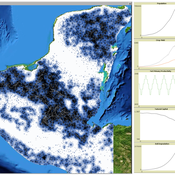
MayaSim: An agent-based model of the ancient Maya social-ecological system
Scott Heckbert | Published Wednesday, July 11, 2012 | Last modified Tuesday, July 02, 2013MayaSim is an agent-based, cellular automata and network model of the ancient Maya. Biophysical and anthropogenic processes interact to grow a complex social ecological system.
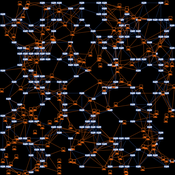
Modeling financial networks based on interpersonal trust
Michael Roos Anna Klabunde | Published Wednesday, May 29, 2013 | Last modified Thursday, November 28, 2013We build a stylized model of a network of business angel investors and start-up entrepreneurs. Decisions are based on trust as a decision making tool under true uncertainty.
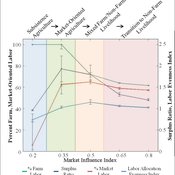
Land-Livelihood Transitions
Nicholas Magliocca Daniel G Brown Erle C Ellis | Published Monday, September 09, 2013 | Last modified Friday, September 13, 2013Implemented as a virtual laboratory, this model explores transitions in land-use and livelihood decisions that emerge from changing local and global conditions.
Last Mile Commuter Behavior Model
Dean Massey Moira Zellner Yoram Shiftan Jonathan Levine Maria Arquero | Published Friday, November 07, 2014 | Last modified Friday, November 07, 2014We represent commuters and their preferences for transportation cost, time and safety. Agents assess their options via their preferences, their environment, and the modes available. The model has policy levers to test impact on last-mile problem.
This is a social trust model for investigating the social relationships and social networks in the real world and in social media.
Life Cycle Cost of Military Manpower Model
Jonathan Ozik Todd Combs | Published Monday, January 05, 2015We demonstrate how Repast Simphony statecharts can efficiently encapsulate the deep classification hierarchy of the U.S. Air Force for manpower life cycle costing.
Peter Diamond's Coconut Model (Heterogeneity and Learning)
Sven Banisch Eckehard Olbrich | Published Monday, May 30, 2016Agent-based version of the simple search and barter economy conceived by Peter Diamond in 1982. The model is also known as Coconut Model.
Displaying 10 of 388 results for "Huw Vasey" clear search