About the CoMSES Model Library more info
Our mission is to help computational modelers develop, document, and share their computational models in accordance with community standards and good open science and software engineering practices. Model authors can publish their model source code in the Computational Model Library with narrative documentation as well as metadata that supports open science and emerging norms that facilitate software citation, computational reproducibility / frictionless reuse, and interoperability. Model authors can also request private peer review of their computational models. Models that pass peer review receive a DOI once published.
All users of models published in the library must cite model authors when they use and benefit from their code.
Please check out our model publishing tutorial and feel free to contact us if you have any questions or concerns about publishing your model(s) in the Computational Model Library.
We also maintain a curated database of over 7500 publications of agent-based and individual based models with detailed metadata on availability of code and bibliometric information on the landscape of ABM/IBM publications that we welcome you to explore.
Displaying 10 of 824 results for "Jon Solera" clear search
Mobility USA (MUSA)
Giangiacomo Bravo Davide Natalini | Published Sunday, December 08, 2013 | Last modified Monday, December 30, 2013MUSA is an ABM that simulates the commuting sector in USA. A multilevel validation was implemented. Social network with a social-circle structure included. Two types of policies have been tested: market-based and preference-change.
Peer reviewed FishMob: Interactions between fisher mobility and spatial resource heterogeneity
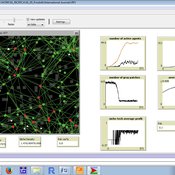
Emilie Lindkvist | Published Wednesday, October 16, 2019 | Last modified Tuesday, June 23, 2020Migration or other long-distance movement into other regions is a common strategy of fishers and fishworkers living and working on the coast to adapt to environmental change. This model attempts to understand the general dynamics of fisher mobility for over larger spatial scales. The model can be used for investigating the complex interplay that exists between mobility and fish stock heterogeneity across regions, and the associated outcomes of mobility at the system level.
The model design informed by the example of small-scale fisheries in the Gulf of California, Mexico but implements theoretical and stylized facts and can as such be used for different archetypical cases. Our methodological approach for designing the model aims to account for the complex causation, emergence and interdependencies in small-scale fisheries to explain the phenomenon of sequential overexploitation, i.e., overexploiting one resource after another. The model is intended to be used as a virtual laboratory to investigate when and how different levels of mobile fishers affect exploitation patterns of fisheries resources.
SiFlo: An Agent-based Model to simulate inhabitants’ behavior during a flood event
Patrick Taillandier Franck Taillandier Pascal Di Maiolo Rasool Mehdizadeh | Published Thursday, July 29, 2021SiFlo is an ABM dedicated to simulate flood events in urban areas. It considers the water flowing and the reaction of the inhabitants. The inhabitants would be able to perform different actions regarding the flood: protection (protect their house, their equipment and furniture…), evacuation (considering traffic model), get and give information (considering imperfect knowledge), etc. A special care was taken to model the inhabitant behavior: the inhabitants should be able to build complex reasoning, to have emotions, to follow or not instructions, to have incomplete knowledge about the flood, to interfere with other inhabitants, to find their way on the road network. The model integrates the closure of roads and the danger a flooded road can represent. Furthermore, it considers the state of the infrastructures and notably protection infrastructures as dyke. Then, it allows to simulate a dyke breaking.
The model intends to be generic and flexible whereas provide a fine geographic description of the case study. In this perspective, the model is able to directly import GIS data to reproduce any territory. The following sections expose the main elements of the model.
User Guide and Templates for RAT-RS (a reporting standard for improving the documentation of data use in agent-based modelling)
Melania Borit Edmund Chattoe-Brown Peer-Olaf Siebers Sebastian Achter | Published Saturday, March 12, 2022The Rigor and Transparency Reporting Standard (RAT-RS) is a tool to improve the documentation of data use in Agent-Based Modelling. Following the development of reporting standards for models themselves, attention to empirical models has now reached a stage where these standards need to take equally effective account of data use (which until now has tended to be an afterthought to model description). It is particularly important that a standard should allow the reporting of the different uses to which data may be put (specification, calibration and validation), but also that it should be compatible with the integration of different kinds of data (for example statistical, qualitative, ethnographic and experimental) sometimes known as mixed methods research.
For the full details on the RAT-RS, please refer to the related publication “RAT-RS: A Reporting Standard for Improving the Documentation of Data Use in Agent-Based Modelling” (http://dx.doi.org/10.1080/13645579.2022.2049511).
Here we provide supplementary material for this article, consisting of a RAT-RS user guide and RAT-RS templates.
Using Agent-Based Modelling and Reinforcement Learning to Study Hybrid Threats
kpadur | Published Friday, September 20, 2024Hybrid attacks coordinate the exploitation of vulnerabilities across domains to undermine trust in authorities and cause social unrest. Whilst such attacks have primarily been seen in active conflict zones, there is growing concern about the potential harm that can be caused by hybrid attacks more generally and a desire to discover how better to identify and react to them. In addressing such threats, it is important to be able to identify and understand an adversary’s behaviour. Game theory is the approach predominantly used in security and defence literature for this purpose. However, the underlying rationality assumption, the equilibrium concept of game theory, as well as the need to make simplifying assumptions can limit its use in the study of emerging threats. To study hybrid threats, we present a novel agent-based model in which, for the first time, agents use reinforcement learning to inform their decisions. This model allows us to investigate the behavioural strategies of threat agents with hybrid attack capabilities as well as their broader impact on the behaviours and opinions of other agents.
Replica of Turchin's (2003) Metaethnic Frontier model
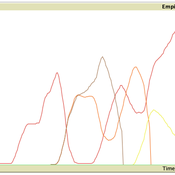
Paul Smaldino | Published Sunday, February 15, 2026In his 2003 book, Historical Dynamics (ch. 4), Turchin describes and briefly analyzes a spatial ABM of his metaethnic frontier theory, which is essentially a formalization of a theory by Ibn Khaldun in the 14th century. In the model, polities compete with neighboring polities and can absorb them into an empire. Groups possess “asabiya”, a measure of social solidarity and a sense of shared purpose. Regions that share borders with other groups will have increased asabiya do to salient us vs. them competition. High asabiya enhances the ability to grow, work together, and hence wage war on neighboring groups and assimilate them into an empire. The larger the frontier, the higher the empire’s asabiya.
As an empire expands, (1) increased access to resources drives further growth; (2) internal conflict decreases asabiya among those who live far from the frontier; and (3) expanded size of the frontier decreases ability to wage war along all frontiers. When an empire’s asabiya decreases too much, it collapses. Another group with more compelling asabiya eventually helps establish a new empire.
Village Ecodynamics Project
ipem | Published Friday, May 13, 2011 | Last modified Saturday, April 27, 2013The Village Project is designed to help archaeologists understand the factors influencing settlement patterns of small-scale agrarian peoples. Although such societies are becoming increasingly rare, they represent the norm throughout most of the Neolithic period the world over.
Collective Decision Making for Ecological Restoration version 2.0
Dean Massey Moira Zellner Cristy Watkins Jeremy Brooks Kristen Ross Lynne M Westphal | Published Wednesday, November 19, 2014CoDMER v. 2.0 was parameterized with ethnographic data from organizations dealing with prescribed fire and seeding native plants, to advance theory on how collective decisions emerge in ecological restoration.
Peer reviewed Garbage can model Excel reconstruction
Smarzhevskiy Ivan | Published Tuesday, August 19, 2014 | Last modified Tuesday, July 30, 2019Reconstruction of the original code M. Cohen, J. March, and J. Olsen garbage can model, realized by means of Microsoft Office Excel 2010
Emerging innovation niches model
Antonio Lopolito Richard Taylor Piergiuseppe Morone | Published Monday, September 22, 2014Objective of our model is to simulate the emergence and operation of a technological niches (TN) in terms of actors’ interaction. A TN can be conceived as protected socio-economic space where radical innovations are developed and tested
Displaying 10 of 824 results for "Jon Solera" clear search